This Chip will Self-Destruct
The U.S. wants to track the location of every AI microchip. And it also wants the power to remotely shut them down. Can the rest of the world stomach the risks?
It wasn’t supposed to be possible. At least not so fast.
China, we were confidently told, was losing the race for AI superiority. It was failing to innovate at the same rate as the U.S. or even the E.U.1 And it didn’t have access to the most advanced microchips. The Biden administration had made sure of that, imposing restrictions on the export of semiconductor technology to the PRC.2 And yet there it was: DeepSeek. This Chinese start-up shocked the world earlier this year by releasing an AI model that can replicate ChatGPT at a fraction of the cost.3 The news sent tech stocks plummeting by more than a trillion dollars.4 And it had everyone asking the same question: how did they do it?
Perhaps we shouldn’t have been so surprised. This certainly wouldn’t be the first time Americans underestimated their foreign adversaries. We are taught from an early age to develop an ironclad superiority complex, one that tells us to ignore all those pesky statistics about falling behind other countries in math and science.5 And the last time I checked China is, wait for it, communist. Surely a country that uses the hammer and sickle logo can’t compete with good-old-fashioned American capitalism. I mean just look at the global market for telecommunication…or electric vehicles…or precious metals…or…OK maybe don’t.6
But arrogance doesn’t explain everything. Because there is still a lingering question of how a Chinese start-up obtained the necessary computing power. The best AI models require the best AI chips. And those chips are primarily made by American companies like Nvidia, AMD, and Google.7 U.S. export controls were supposed to prevent these companies from selling their most advanced wares to China. But those controls do not appear to be working. It has been estimated that approximately 140,000 advanced AI chips were smuggled into China in 2024.8 That would suggest smuggling accounts for 6% of China’s total AI inference capacity and 10% of its training capacity.9 Higher end estimates would push those numbers to 30% and 40%.10
This appears, at first glance, like an impossible problem to solve. The U.S. Bureau of Industry and Security (BIS), a chronically underfunded agency responsible for export control enforcement, is not going to inspect every chip.11 And they can only observe a fraction of the global semiconductor supply chain. As we have discussed, goods can be re-exported through third countries to evade restrictions. And, indeed, there is evidence to suggest that China’s obtainment of advanced AI chips relies on their illicit transshipment through countries like Singapore.12
But maybe the solution is not about external enforcement. Perhaps the answer lies instead within the chip itself. What if we were to infuse every AI chip with a location tracking device, one that allowed us to monitor its movement across the globe? And what if we were to also add a feature that remotely disables the chip — an emergency self-destruct button — whenever it is misused? This is not science fiction. It is, in fact, a fast growing area of research on semiconductor technology.13 And a bipartisan group of lawmakers, led by Senator Tom Cotton, have introduced the Chip Security Act to encode location verification into advanced AI chips.14
These mechanisms are not just about preventing illicit trade. They are also essential to international security. Or at least that is the argument of a new working paper by Dan Hendrycks, Eric Schmidt, and Alexandr Wang.15 The paper has attracted attention for its concept of Mutual Assured AI Malfunction (MAIM).16 Less discussed is the authors’ ideas on nonproliferation. Likening AI chips to weapons of mass destruction (WMDs), they contend that location tracking and other firmware mechanisms can prevent them from falling into the hands of rogue actors.
But what this discussion overlooks are the power implications. Because allowing the BIS (or U.S. companies acting under its authority) to track the movement of AI chips and remotely disable their functionality is not a benign strategy. It represents instead an enormous transfer of power to one actor: America. Is the world really going to sit back and allow the U.S. to exert control over the world’s most valuable chips? And is there anything they can do to stop it?
Kill Switch
This is not the first time concerns have been expressed about the remote disablement of strategic weaponry. Rumors recently swirled around whether the F-35, an American-made fighter jet used by many Western allies, contains a secret “kill switch” controlled by the U.S. military. No such switch exists.17 But there are various components of the supply chain controlled by the U.S. As Henry Farrell and Abraham Newman summarize in a recent piece for Wired:
Sources tell us that there is no such kill switch on the F-35, per se. But the underlying anxiety is not unfounded. There is, as one former US defense official described it, a “kill chain” that is “essentially controlled by the United States.” Complex weapons platforms require constant maintenance and software updates, and they rely on real-time, proprietary intelligence streams for mapping and targeting. All that “flows back through the United States,” the former official said, and can be blocked or turned off.18
This is not exactly reassuring if you are a European defense minister (or an F-35 pilot worried about a mid-maneuver software failure). And that is precisely why the EU’s buzziest buzz word is “digital sovereignty.” Faced with an adversarial U.S., Europe is seeking to reduce its dependence on American technology.19 That includes creating its own independent semiconductor ecosystem.20
Europe does have certain advantages. It is host to ASML, the world’s sole producer of extreme ultraviolet (EUV) lithography systems. EUV is the process by which advanced chips are actually created. And as I covered in a previous post, ASML has established a monopoly on the world’s most advanced EUV machines. But the EU hasn’t historically employed those machines to make chips domestically. Rather, ASML primarily exports its EUV systems (at up to $380 million per unit) to foreign manufacturers, who then turn around and sell their chips back to Europe.21
The region is taking steps to reverse this dependency. The EU Chips Act, for example, commits €43 billion to help grow Europe’s share of the global manufacturing market from 10% to 20% by 2030.22 And large players like TSMC are establishing European factories.23 Nevertheless, estimates suggest that the EU is on track to achieve only an 11.7% market share by the end of the decade.24 As the European Court of Auditors summarized in a scathing report, “The Chips Act is likely to be insufficient” and the Commission needs “an urgent reality check.”25
Policymakers are reportedly working on a Chips Act 2.0.26 And, from the perspective of the EU, it cannot come soon enough. Because dependency on foreign imports is one thing. But if the U.S. actually pushes forward with encoding AI chips with tracking mechanisms, it poses an entirely new level of risk. One where “kill switches” are not just exaggerated internet rumors but, instead, an all too real threat.
Tracking the Chips
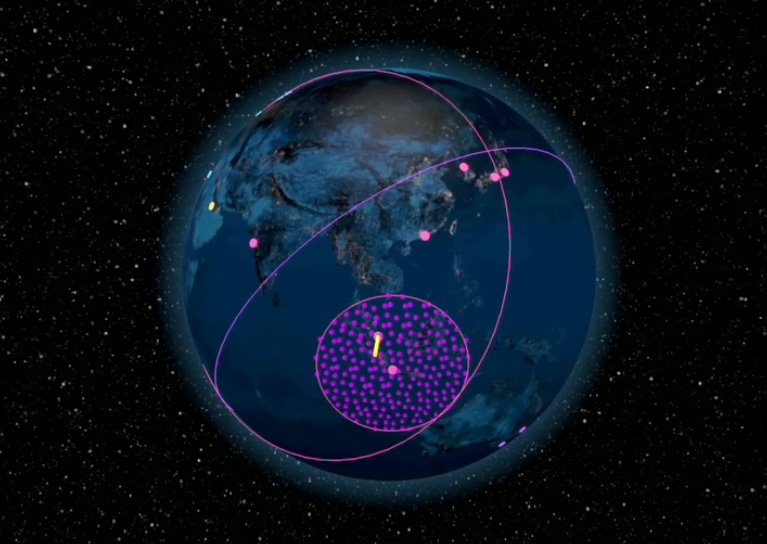
Some of this technology is already in place. Nvidia has confirmed that its AI chips can collect and transmit geolocation data.27 And one start-up has demonstrated that the Nvidia H100 chip can be programmed to send pings (essentially electronic messages) to Google datacenters all over the world.28 The response time from each datacenter provides an estimate of its distance from the chip, thereby allowing one to triangulate its position to within 500 kilometers. And that’s all based on only “publicly available, off-the-shelf offerings from Google and Nvidia.”29
We know that much higher rates of accuracy are achievable.30 And that is precisely what Hendrycks, Schmidt, and Wang envision in their WMD-inspired proposal:
By measuring signal delays from multiple landmarks, a chip can verify its location within tens to hundreds of kilometers—enough to determine whether it is in the correct country. If a chip moves to an unauthorized area, it can automatically deactivate or limit its functionality. This makes it more challenging for unauthorized parties to smuggle or misuse AI chips, as relocating them without detection becomes more difficult.31
Location tracking is not the only possible security feature. The authors also observe that chips can be outfitted with tamper-proof seals and programmed to only work with other pre-approved chips.32 But the real killer application here is tracking chips and remotely disabling their functionality.
One group of U.S. lawmakers appears to agree. The Chip Security Act would mandate that exporters perform surveillance on their AI chips and report certain events to the BIS. That includes any chips which are detected in unauthorized locations or found to be in possession of unexpected users.33 This places the primary monitoring burden on private firms. But that doesn’t mean they are completely in control. The bill also specifies that the Secretaries of Commerce and Defense will determine which types of surveillance mechanisms chip exporters should employ.34
It is not entirely clear what mandate this bill would afford to the BIS. What is stated is that the Secretary of Commerce, Howard Lutnick, would be granted sweeping powers to carry out his assessment. That includes verifying the ownership, location, and end-users of advanced AI chips.35 It is not hard to imagine this morphing into the creation of a database accessible to U.S. authorities. But even without such a database, the U.S. government could easily subpoena exporters for geolocation data. And in times of war, it could plausibly direct those firms to remotely disable chips.36
This is not quite what Hendrycks, Schmidt, and Wang envision. They view these tools as an opportunity for “bitter adversaries” to undertake the “shared imperative of avoiding catastrophes that serve no one's ambitions.”37 This is admirable. But what is more likely is that they inadvertently facilitate coercive power. And the IR literature has developed a phrase for this sort of thing.
Weaponized Interdependence
But wait, readers familiar with the semiconductor market might be thinking, the U.S. doesn’t dominate chip manufacturing.38 Nor does it control the market for materials (silicon) or production machines (ASML).39 And that’s all true. But what America does dominate is the design of AI chips.40 The reason Nvidia is the world’s most valuable company is that it holds somewhere between 70% and 95% of the global market for AI chip design.41 Therefore, the design choices it makes — including whether to add geolocation sensors or self-destruction mechanisms — flow downstream through the winding tributaries of the semiconductor supply chain.42
And this renders it ripe for weaponization. Specifically, what Farrell and Newman refer to as weaponized interdependence.43 This concept, which has been referenced by both Trump officials and European Commission President Ursula von der Leyen, reflects the strategic opportunities afforded by economic networks.44 Per the authors, states that control key “hubs” in these networks can exploit their position to engage in coercive actions against geopolitical adversaries.45
Take, for example, the internet. Approximately 70% of worldwide internet traffic flows through “Data Center Alley” in Northern Virginia.46 Therefore, Northern Virginia is the central “hub” connecting the world wide web. And that creates strategic opportunities only available to America. Specifically, it has allegedly allowed the National Security Agency (NSA) to monitor global telecommunication.47
What this example demonstrates is that opportunities for weaponization are made possible by asymmetric networks. There must be a structural imbalance, one where central “hubs” are only available to privileged actors.48 Not every step of the AI chip supply chain satisfies this condition. But as another set of scholars have shown, the U.S. can still exploit its asymmetric position in chip design:
…targeting [Chinese telecommunications giant] Huawei, the U.S. restricted the export of foreign-produced semiconductors made using American software or technology. As a result of this change, companies in Taiwan and South Korea faced being cut off from U.S. software, core intellectual property and manufacturing equipment if they continued to supply Huawei. It was this measure, taken in August 2020, that significantly disrupted Huawei's supplies of semiconductors.49
Why was the U.S. targeting Huawei? Because American officials fear that its global expansion allows China to spy on telecommunication.50 How dare they! We all know that’s our job.51 And they were able to choke off Huawei’s access to semiconductors by threatening to withhold products from third-party suppliers. But what is now being discussed is a whole new level of control. One where America would play puppet master, monitoring each and every advanced AI chip from behind the scenes and pulling their strings at a moment’s notice.
Implementing such features is, of course, easier said than done. It would require that the U.S. (or private companies) establish stations around the world to triangulate chip locations.52 Geopolitical adversaries may not appreciate this. And they could connect their chips to private internet networks to disrupt the process.53 And while it would be extremely difficult to remove the chip’s geolocation features, China would have plenty of incentives to try.54 But keeping in mind everything we have learned about the NSA, would you bet against them succeeding?
The real Achilles heel is the underlying economic network. This entire proposition rests on an assumption of asymmetry. Namely, that Nvidia and other American firms continue to dominate the market for advanced AI chip design. But China is not sitting on its hands. It is, instead, actively pushing to create domestic alternatives to Nvidia (and ASML).55 If they succeed, any coercive power the U.S. obtains through AI chip surveillance would naturally dissipate.
And, indeed, America should be wary of overconfidence. Looking at Nvidia’s revenue today, it is difficult to imagine them losing their AI dominance. But that is also what everyone thought about ChatGPT before DeepSeek crashed the party. The reality is that China is making headway. And there is a very real possibility it overtakes Silicon Valley in the not-too-distant future. If that happens, it won’t just be Europe concerned about its digital sovereignty. America will also be looking over its shoulder, disquietly wondering if their chips, too, are about to implode.
Stanford Institute for Human-Centered AI, Artificial Intelligence Index Report 2024.
Erich Grunewald & Tim Fist, Countering AI Chip Smuggling Has Become a National Security Priority. This is the author’s median estimate.
Ibid.
Ibid.
Permanent Subcommittee on Investigations, The U.S. technology fueling Russia’s war in Ukraine: Examining the Bureau of Industry and Security’s enforcement of semiconductor export controls. See also Henry Farrell on America's plan to control global AI.
U.S. House Select Committee on the Chinese Communist Party, DeepSeek Unmasked.
Scott J Mulligan, Can “Location Verification” Stop AI Chip Smuggling?
Dan Hendrycks, Eric Schmidt, Alexandr Wang, Superintelligence Strategy.
See, e.g., Peter Wildeford and Oscar Delaney, Mutual sabotage of AI probably won’t work.
David Cenciotti and Stefano D'Urso, The F-35 ‘Kill Switch’: Separating Myth from Reality.
Henry Farrell and Abraham L. Newman, The Enshittification of American Power.
European Commission, 2022 State of the Union Address by President von der Leyen.
Ciani, A. and Nardo, M., The position of the EU in the semiconductor value chain: evidence on trade, foreign acquisitions, and ownership, European Commission, 2022, JRC129035.
Sujai Shivakumar, Charles Wessner, and Thomas Howell, A World of Chips Acts: The Future of U.S.-EU Semiconductor Collaboration.
European Court of Auditors, Special Report: The EU’s strategy for microchips.
Ibid.
Chiara Malaponti, Chips on the menu: How the EU can get its act together on semiconductors.
Samuel Hammond, The Chip Security Act: A Bipartisan Solution to Chip Smuggling.
Ulyssean and Tinfoil, Ping-based location. Referenced in Samuel Hammond, The Chip Security Act: A Bipartisan Solution to Chip Smuggling.
Ibid.
Sheng et al., BFT-PoLoc: A Byzantine Fortified Trigonometric Proof of Location Protocol using Internet Delays. Quoted in Scott J Mulligan, Can “Location Verification” Stop AI Chip Smuggling? See also Asher Brass & Onni Aarne, Location Verification for AI Chips.
Dan Hendrycks, Eric Schmidt, Alexandr Wang, Superintelligence Strategy, p. 20.
Ibid.
[they shall] “…conduct an assessment to identify what additional mechanisms, if any, should be added to the primary chip security mechanisms…if the Secretary identifies any such mechanism, develop requirements for outfitting covered integrated circuit products with that mechanism.”
“(c) Enforcement authority.—In carrying out this section, the Secretary may—
(1) verify, in a manner the Secretary determines appropriate, the ownership and location of a covered integrated circuit product that has been exported, reexported, or in-country transferred to or in a foreign country;
(2) maintain a record of covered integrated circuit products and include in the record the location and current end-user of each such product; and
(3) require any person who has been granted a license or other authorization under the Export Control Reform Act of 2018 to export, reexport, or in-country transfer a covered integrated circuit product to provide the information needed to maintain the record.”
This is likely easier said than done. But would you put it past the world’s most powerful AI companies?
Dan Hendrycks, Eric Schmidt, Alexandr Wang, Superintelligence Strategy, p. 21.
Beaumier, Guillaume, and Madison Cartwright. "Cross-network weaponization in the semiconductor supply chain." International Studies Quarterly 68, no. 1 (2024): sqae003.
Ibid.
Beaumier, Guillaume, and Madison Cartwright. "Cross-network weaponization in the semiconductor supply chain." International Studies Quarterly 68, no. 1 (2024): sqae003.
Henry Farrell, Abraham L. Newman; Weaponized Interdependence: How Global Economic Networks Shape State Coercion. International Security 2019; 44 (1): 42–79. doi: https://doi.org/10.1162/isec_a_00351
Newman, Abraham L., Henry Farrell, and Daniel W. Drezner. "17. Weaponized Interdependence and Networked Coercion: A Research Agenda." The uses and abuses of weaponized interdependence (2021): 305-322.
Henry Farrell, Abraham L. Newman; Weaponized Interdependence: How Global Economic Networks Shape State Coercion. International Security 2019; 44 (1): 42–79. doi: https://doi.org/10.1162/isec_a_00351. Also see Underground Empire.
Henry Farrell, Abraham L. Newman; Weaponized Interdependence: How Global Economic Networks Shape State Coercion. International Security 2019; 44 (1): 42–79. doi: https://doi.org/10.1162/isec_a_00351. Also see Underground Empire.
I have a working paper exploring what opportunities might also be available in more symmetrical networks — watch this space.
Beaumier, Guillaume, and Madison Cartwright. "Cross-network weaponization in the semiconductor supply chain." International Studies Quarterly 68, no. 1 (2024): sqae003.
Check out Eva Dou’s fantastic House of Huawei.
Ibid.
Asher Brass & Onni Aarne, Location Verification for AI Chips.
Ibid.
Scott J Mulligan, Can “Location Verification” Stop AI Chip Smuggling?


Fascinating. Now I have to update my intelligence understanding.
Great post! Forwarded and shared to other end readers!